Enabling Anonymous SIP Access and SIP URI Calling into Your XiVO PBX
Photo credit: FingerMedium/GettyImages
WARNING: This is very dangerous! Only implement this if there is no other way for folks to reach you by phone. Anonymous SIP URI access to your server means anyone with an Internet connection
worldwide can not only call your server, but they also can attempt to register a SIP account to any SIP extension on your PBX and they also can attempt to place outbound calls through your PBX. The only thing standing in their way are your SIP account passwords! What follows is an approach to SIP URI access that minimizes (BUT DOES NOT ELIMINATE) the risk.
The safest and recommended way to implement SIP URI access to your PBX does not expose your server to anonymous SIP access. It is documented in this Nerd Vittles tutorial. You've been warned!
A word about the methodology that follows. To minimize the risk of compromising your server, use incredibly secure passwords for all of your user, line, and trunk accounts. Do this
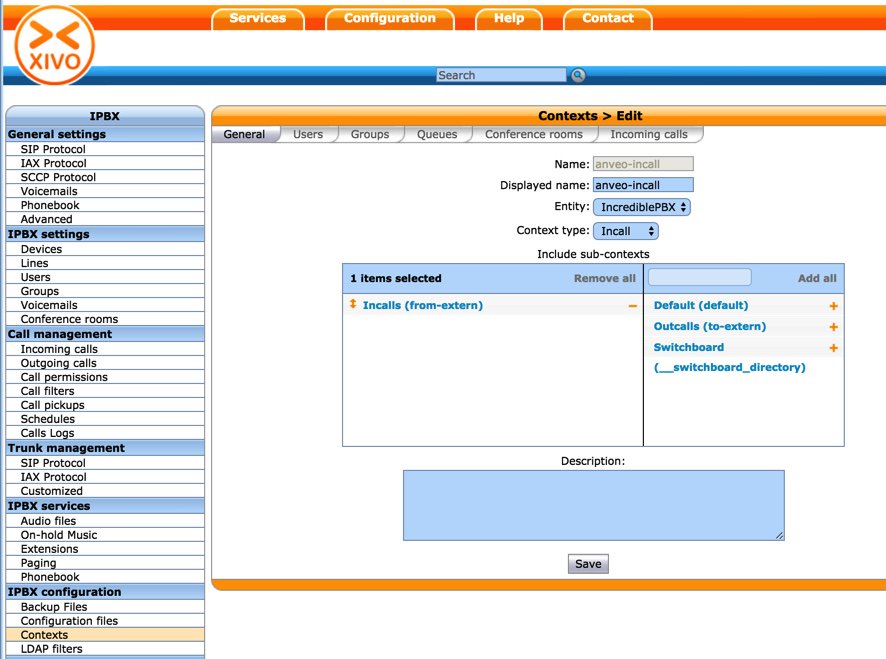
before proceeding. Also make certain that your server has a difficult-to-guess fully-qualified domain name (FQDN) as this will provide some security through obscurity. We will block outgoing SIP calls that attempt to use the actual IP address of your server, and we will block incoming SIP URI calls made to the IP address of your server. Use trunk providers on this PBX that have a very low account balance with NO recurring credit card refresh. Google Voice accounts with a zero balance are perfect. If someone does manage to make calls, it will not hurt your wallet. Do NOT use IAX trunks. This hasn't been tested or secured at all for use with IAX trunks. Add passwords to all Asterisk applications that matter, e.g. blacklisting callers, accessing AsteriDex to place calls, conference apps, IVRs, etc.
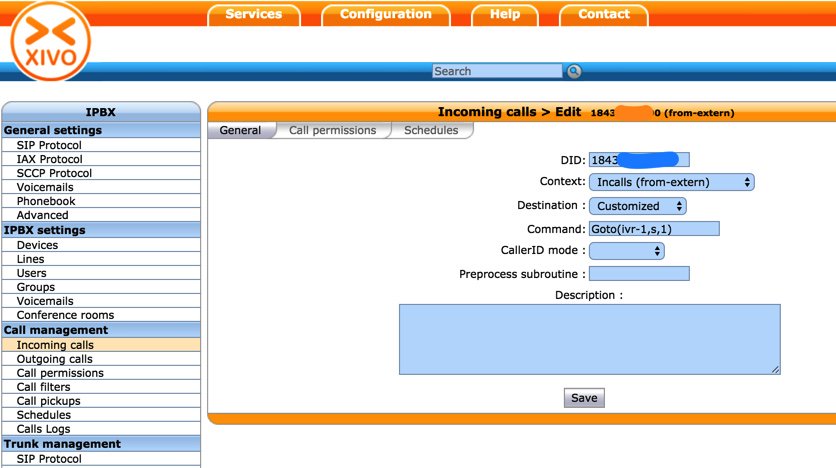
What does SIP URI access provide to the caller? It means the caller that knows your FQDN can place calls to every extension on your PBX, to every incoming DID defined on your PBX, and to almost every Asterisk feature code enabled on your PBX. It also means any anonymous user with either your FQDN or IP address can attempt to register to any SIP account on your PBX. All they'll need is the account name and password. If a user successfully registers to your PBX using the IP address of your server (as opposed to your FQDN), we will block them from making outbound SIP calls. If any of this frightens you, turn back now!!
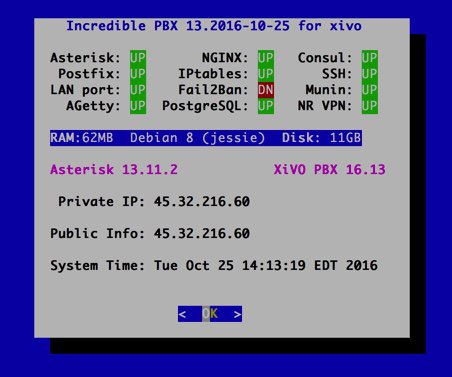
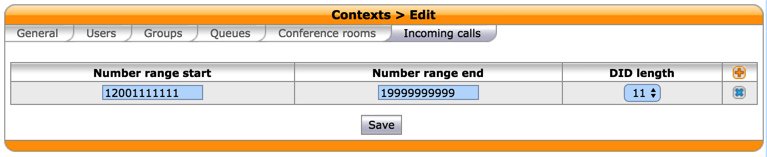
1. Activate
Accept Unauthenticated Calls (General tab) and set
Context to
In-Calls (Default tab) in
IPX -> General Settings -> SIP Protocol.
2. Add IP address protection and modify failure routine in xivo-subrgbl-did and xivo-subrgbl-outcall contexts:
2.a. Edit
/etc/asterisk/extensions_extra.d/cid-superfecta.conf and replace [xivo-subrgbl-did] context with the following:
Code:
[xivo-subrgbl-did]
exten = s,1,NoOp(### DID Incoming Call Subroutine ###)
same = n,GotoIf($["${XIVO_SRCNUM:0:3}" != "001"]?leaveitalone)
same = n,Set(XIVO_SRCNUM=${XIVO_SRCNUM:-10})
same = n,Set(CALLERID(num)=${XIVO_SRCNUM})
same = n(leaveitalone),NoOp(Calling FROM: ${XIVO_SRCNUM})
same = n,Noop(SIP TO: ${SIP_HEADER(TO)})
same = n,Noop(SIP FROM: ${CUT(SIP_HEADER(FROM),>,1)}>)
same = n,Set(NUMTEST=${SIP_HEADER(TO):-2:1})
same = n,GotoIf(gv$["${NUMTEST}" = "gv"]?gv)
same = n,GotoIf($["${NUMTEST}" < "A"]?byebye)
same = n(gv),NoOp(Blacklist: ${DB(blacklist/${XIVO_SRCNUM})})
same = n,NoOp(Whitelist: ${DB(whitelist/${XIVO_SRCNUM})})
same = n,GotoIf($[${LEN(${DB(whitelist/${XIVO_SRCNUM})}))} > 1]?keepon)
same = n,GotoIf($[${LEN(${DB(blacklist/${XIVO_SRCNUM})}))} > 1]?byebye)
same = n(keepon),GoSub(cid-superfecta,s,1)
same = n(return),Return()
same = n(byebye),Answer
;same = n,Congestion
same = n,Zapateller
same = n,Zapateller
same = n,Hangup
same = n,Return()
2.b. Edit
/etc/asterisk/extensions_extra.d/out-calls.conf and replace [xivo-subrgbl-outcall] context with the following:
Code:
[xivo-subrgbl-outcall]
exten = s,1,NoOp(### DID Outgoing Call Subroutine ###)
same = n,NoOp(Calling FROM: ${XIVO_SRCNUM})
same = n,NoOp(Calling TO: ${EXTEN})
same = n,Noop(XIVO SRC NUMBER=${XIVO_SRCNUM})
same = n,Noop(XIVO DST NUMBER=${XIVO_DSTNUM})
same = n,Noop(XIVO DST ID=${XIVO_DSTID})
same = n,Noop(XIVO USR ID=${XIVO_USRID})
same = n,Noop(SIP TO: ${SIP_HEADER(TO)})
same = n,Noop(SIP FROM: ${SIP_HEADER(FROM)})
same = n,Set(NUMTEST=${SIP_HEADER(TO):-2:1})
same = n,GotoIf(gv$["${NUMTEST}" = "gv"]?return)
same = n,GotoIf($["${NUMTEST}" < "A"]?byebye)
same = n(return),Return()
same = n(byebye),Hangup
same = n,Return()
3. Secure Asterisk apps using Asterisk's Authenticate function. Insert the line below just after the Answer and Wait() lines in
/etc/asterisk/extensions_extra.d/app-blacklist.conf contexts: [app-blacklist-add], [app-blacklist-remove], and [app-blacklist-last] using a very secure PIN to replace 90210:
Code:
exten => s,n,Authenticate(90210)
4. Do the same for any contexts you wish to protect in
/etc/asterisk/extensions_extra.d/xivo-extrafeatures.conf.
5. Reload Asterisk dialplan:
asterisk -rx "dialplan reload"
6. By default, the SIP port (UDP 5060) is only accessible from whitelisted IP addresses. We're now going to open the IPtables floodgate for UDP 5060 so that anonymous SIP calls can reach your PBX. Edit /etc/iptables/rules.v4. Just above the COMMIT line at the end of the file, insert the following entry:
Code:
-A INPUT -p udp -m udp --dport 5060 -j ACCEPT
Save the file and then restart IPtables:
iptables-restart
7.
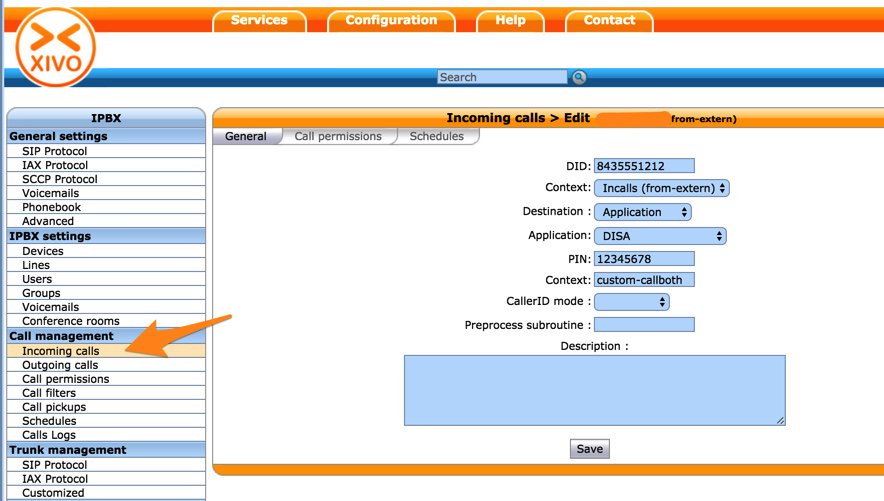
Test, test, test. From an IP address not otherwise whitelisted on your PBX, place anonymous SIP calls to every extension on your PBX and to every DID listed in your Incoming Calls list. Use both the IP address of your PBX and also the FQDN associated with your PBX. Also place calls to all of the Nerd Vittles and XiVO apps that could do you harm, i.e. voice dialing, speed dialing, blacklist callers, etc. Complete list of potentially hazardous dial codes is at the end of this
Nerd Vittles article.
For the Geeks and Nerds: The methodology to weed out SIP URI calls made to an IP Address instead of an FQDN takes advantage of a careful parsing of the TO SIP Header. You will note that the next-to-the-last character in this SIP header will always be a letter for an FQDN and will always be a number for an IP address. Thus, we can test where the alphanumeric character fits in the ASCII sort order to determine whether the incoming call is being routed to an IP address or an FQDN. And, by the way, for incoming Google Voice calls, this result will always be NULL.