Ward, well noted, I am not well caught up

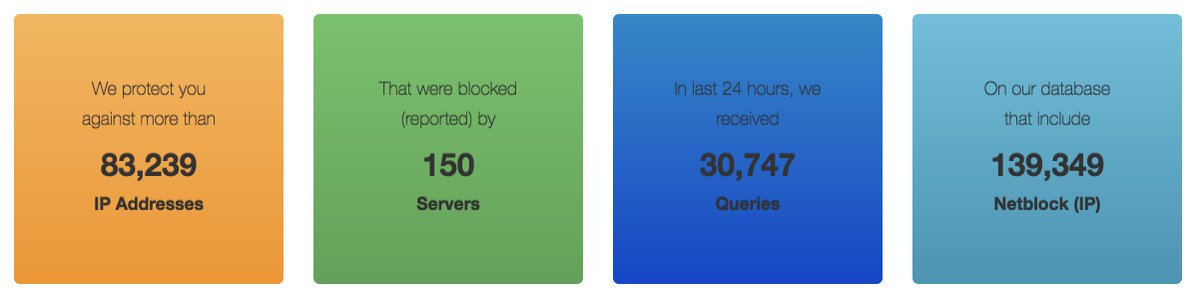
So if anyone has noted , if there is one bad apple in the basket it is likely that there are a lot more soon. If you use ipset then here is a script I wrote that needs ipset > 6.1 and ipwhois ("pip install --upgrade ipwhois") and jq
It is intended to look up the underlying network of an ip and add that to an ipset of your choice
#!/bin/bash
if [[ ! $1 ]];then echo "Usage: $(basename $_) hostname|ip ipset";exit;fi
IP=$1
echo $IP
IPSET=$2
[ $IPSET ]||IPSET='chain_DENY'
[[ $IP =~ ^[0-9\.].* ]]||IP=$(getent ahosts $IP|grep STREAM|head -1|cut -d ' ' -f1)
ipset create -exist $IPSET hash:net comment 2>/dev/null
ipset test $IPSET $IP 2>/dev/null&&echo "already there"&&exit
JSON=$(python /usr/local/bin/ipwhois_cli.py --addr $IP --json --disallow_permutations 2>/dev/null )
[[ $JSON ]] || { echo $JSON ; exit; }
ENTITY=$(echo $JSON|jq '.entities[0]')
NAME=$(echo $JSON|jq ".objects.$ENTITY.contact.name"|sed 's/"//g')
CIDR=$(echo $JSON|jq ".network.cidr"|sed 's/"//g')
CCODE=$(echo $JSON|jq ".asn_country_code"|sed 's/"//g')
NETNAME=$(echo $JSON|jq ".network.name"|sed 's/"//g')
REGISTRY=$(echo $JSON|jq ".asn_registry"|sed 's/"//g')
#for csf
echo "$CIDR # $CCODE $REGISTRY $NETNAME ($NAME)"
# >> /etc/csf/csf.allow
#or whatever
echo "ipset -exist add $IPSET $CIDR comment \"$CCODE $REGISTRY $NETNAME $NAME\""
ipset -exist add $IPSET $CIDR comment "$CCODE $REGISTRY $NETNAME $NAME"
exit
It was originally written for csf with fail2ban actions driving the script so it defaults to the ipset chain_DENY but you can call it with whatever ipset name you want I commented out that but obviously it can be modified.
A caveate is that it will likely sooner or later block large chunks of DigitalOcen,Vultr,AWS etc. so if you yourself exist in such a name space add your own ip to a higher priority allow set.
JM2CAE