Chris Sweeney
Guru
- Joined
- May 23, 2013
- Messages
- 223
- Reaction score
- 28
freepbx.org/node/92822 <--read full text here
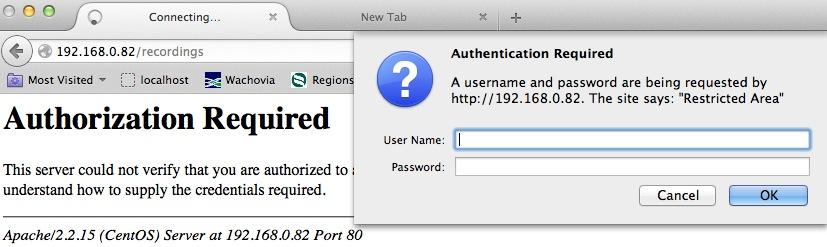
We have been made aware of a critical Zero-Day Remote Code Execution and Privilege Escalation exploit within the legacy “FreePBX ARI Framework module/Asterisk Recording Interface (ARI)”. This affects any user who has installed FreePBX prior to version 12, and users who have updated to FreePBX 12 from a prior version and did not remove the legacy FreePBX ARI Framework module.
This exploit allows users to bypass authentication and gain full “Administrator” access to the FreePBX server when the ARI module is present, which may then be used to grant the attacker full remote code execution access as the user running the Apache process.
We have released updates for users on FreePBX versions 2.9, 2.10, 2.11 and 12 per our security policy which covers releases that have come out over the last 3.5 years. Versions 2.8 and prior can be easily updated to 2.9 or higher through Module Admin which will remove the vulnerability. Versions 2.11 and 12 are the only officially supported versions of FreePBX but we always apply security patches to the two prior versions as well.
Users prior to FreePBX 12 should update immediately.
FreePBX 12 users should disable and uninstall the legacy FreePBX ARI Framework module and switch to the new User Control Panel, which is not to be confused with the previous ‘User Control Panel Tab’.
Please note that indications of a compromised system include the presence of an “System Admin Dashboard” also called “admindashboard” module, the files c2.pl and/or c.sh.
We have been made aware of a critical Zero-Day Remote Code Execution and Privilege Escalation exploit within the legacy “FreePBX ARI Framework module/Asterisk Recording Interface (ARI)”. This affects any user who has installed FreePBX prior to version 12, and users who have updated to FreePBX 12 from a prior version and did not remove the legacy FreePBX ARI Framework module.
This exploit allows users to bypass authentication and gain full “Administrator” access to the FreePBX server when the ARI module is present, which may then be used to grant the attacker full remote code execution access as the user running the Apache process.
We have released updates for users on FreePBX versions 2.9, 2.10, 2.11 and 12 per our security policy which covers releases that have come out over the last 3.5 years. Versions 2.8 and prior can be easily updated to 2.9 or higher through Module Admin which will remove the vulnerability. Versions 2.11 and 12 are the only officially supported versions of FreePBX but we always apply security patches to the two prior versions as well.
Users prior to FreePBX 12 should update immediately.
FreePBX 12 users should disable and uninstall the legacy FreePBX ARI Framework module and switch to the new User Control Panel, which is not to be confused with the previous ‘User Control Panel Tab’.
Please note that indications of a compromised system include the presence of an “System Admin Dashboard” also called “admindashboard” module, the files c2.pl and/or c.sh.